The rise of quantum algorithms that can compromise modern cryptography has led to global efforts in researching stronger security measures.
Today cryptographic schemes rely on solving computationally difficult mathematical problems, but they are at risk of being broken by computational attacks bring by fully working quantum computers because they can leverage quantum algorithms, such as Shor’s [1] algorithm, which can efficiently factor large numbers and solve the discrete logarithm problem using quantum mechanics.
As a result, a quantum computer with a functional number of qubits could potentially break the encryption used in many secure communication protocols so as the one used for online banking, e-commerce, and in general on sensitive data transmission.
To mitigate these risks quantum-mechanical laws themselves offer security against adversaries using quantum computers[2].
This also is a driving force behind the development of a quantum internet. Quantum Key Distribution (QKD) [3] is the most advanced quantum technology, allowing secure communication over public channels. However, in the realm of digital payments, new security threats emerge when customers interact with untrusted parties. In such cases, a binding commitment between the customer, merchant, and bank/payment network is necessary to ensure transaction validity.
While QKD is not suitable for providing information-theoretic security in this scenario, alternative quantum solutions need to be established as well. Device-independent versions of QKD, which do not assume trusted quantum sources or detectors, are also inadequate as the untrusted parties handle the final classical output.[4]
Previous studies have explored the use of quantum light to address issues such as banknote counterfeiting and double-spending with tokens or credit cards. However, implementing quantum-based money in everyday situations is technologically demanding. It requires the ability to store quantum states for extended periods, which exceeds the current capabilities of state-of-the-art quantum storage times that typically range from microseconds to minutes.[5]
Prof. Philip Walther and his research team at the University of Vienna have showcased[6] the ability of quantum properties in light particles, or photons, to provide unconditional security for digital payments. In their experiment, they demonstrated that transactions cannot be duplicated or tampered with by malicious entities, ensuring the privacy of user data.
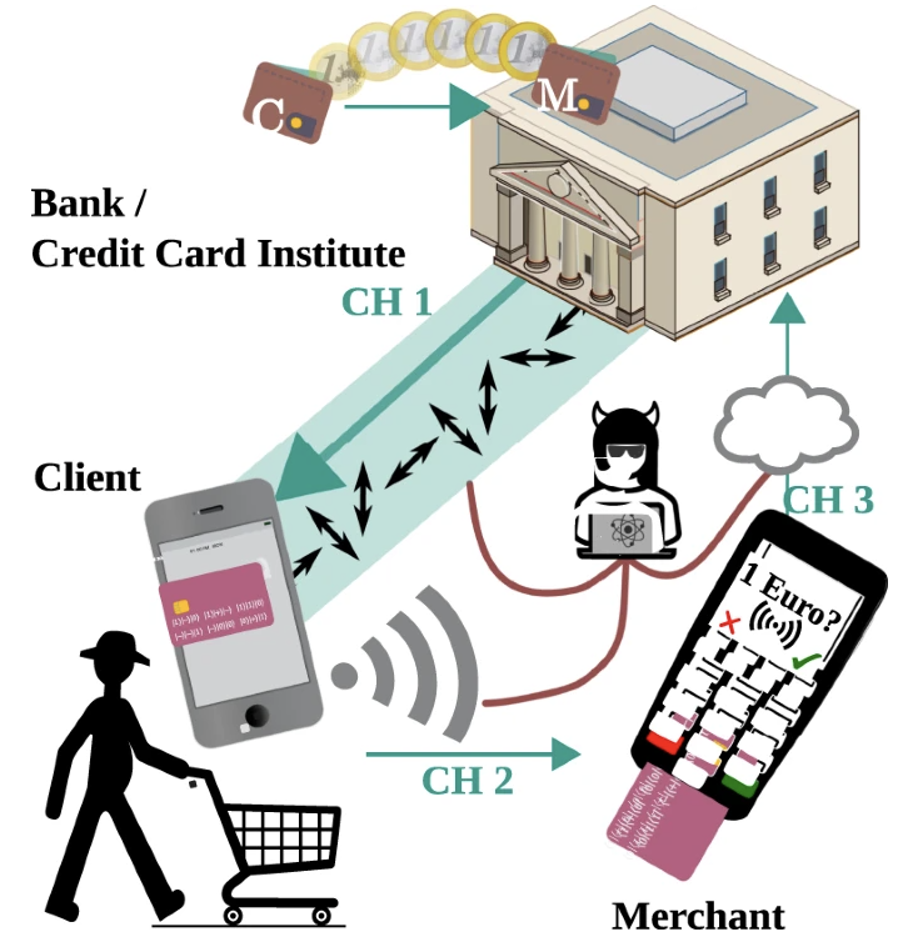
FIGURE: 1 Quantum digital payment REF: SCHIANSKY, Peter, et al. Demonstration of quantum-digital payments. arXiv preprint arXiv:2305.14504, 2023.
FIGURE: 1 Quantum digital payment REF: SCHIANSKY, Peter, et al. Demonstration of quantum-digital payments. arXiv preprint arXiv:2305.14504, 2023.
The researchers achieved absolute security for digital payments by replacing classical cryptographic techniques with a quantum protocol that leverages single photons [7] In this protocol, the client shares a classical code, known as a cryptogram, with the payment provider (e.g., a bank or credit card company) during a typical digital payment transaction.
Instead of using classical methods, the payment provider in the quantum protocol sends specially prepared single photons to the client to generate the cryptogram. The client measures these photons during the payment process, with the measurement settings depending on the transaction parameters. As quantum states of light cannot be replicated, the transaction can only occur once. Furthermore, any deviation from the intended payment alters the measurement outcomes, which are verified by the payment provider, ensuring unconditional security for digital payments.
This achievement will allow us to step into a new era of security where quantum powers pave the way. This solution shatters limitations, leaving behind the need for long-term quantum storage and reliance on trusted agents or authenticated channels. With near-term technology, it is possible to unlock the potential of quantum-enabled security, redefining what’s possible and ensuring a safer digital world
References
[2] Kimble, H. Jeff. “The quantum internet.” Nature 453.7198 (2008): 1023-1030.
[3]Yuen, Horace P. “Security of quantum key distribution.” IEEE Access 4 (2016): 724-749.
[6]https://www.nature.com/articles/s41467-023-39519-w
[7]https://phys.org/news/2023-07-quantum-physicists-unconditionally-digital-payments.html